- Executive Offense
- Posts
- 🔴 Executive Offense Issue #9 - Mobile Application Hacking Part 2
🔴 Executive Offense Issue #9 - Mobile Application Hacking Part 2
Mobile Application Hacking Part 2
EO is a security newsletter that focuses on the intersection between offensive security and security strategy. Sometimes hacker-ish, sometimes CISO-ish. Very blazer over the t-shirt type of vibe…
Welcome back to part 2 of mobile hacking!
/ Interview w Joel Margolis 🔥🔥🔥

This week I thought I’d bring in a friend for some video content. Below is private link for an off-the-cuff technical chat with Joel (aka teknogeek) one of the worlds best mobile hackers. He also happens to be a host of the acclaimed podcast, Critical Thinking, which I highly reccomend. Critical Thinking Podcast, Critical Thinking Discord.
Check it out below! So much good knowledge dropped! (You must be subscribed to see this content)
Some of Joel’s suggested links:
Show note: check out Objection by Sensepost and the cheatsheet by hacktricks!

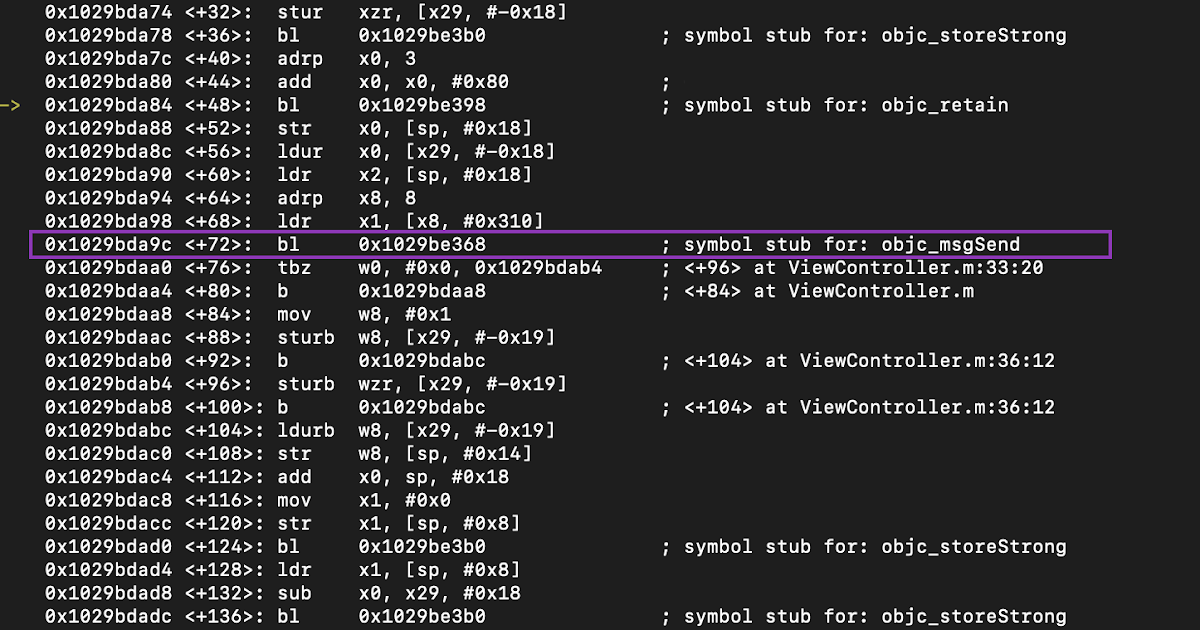
/ Reverse Engineering
As discussed, a lot of the main attack surface for mobile applications lives on the api these days. However, there are instances where exploiting mobile applications can be stage one in a longer set of exploits against an actual phone or needed to reverse engineer app logic.
If you want to dive into reverse engineering and patching iOS applications and exploits related to mobile applications, @inversecos has some good beginner guides on these topics:
In addition to Lina, Maddie Stone has a STELLAR free workshop on Android reverse engineering. It’s a must take:
If you like this content, consider checking out my full 2 day course for pentesters, bug hunters, and red teamers!
/ Creators Spotlight on Hacking APIs
As I mentioned before, a lot of mobile application assessment is assessing the APIs. One of my newer favorite content creators here is Dana Epp, who has been on fire posting a bunch of articles pertaining to API exploitation and testing. Check out his blog for all the goods.

This is not to overshadow the last two years of epic research that has been publicized into books like "Hacking APIs" with Corey Ball and Nick Aleks "Black Hat GraphQL"
/ Vulnerable Apps to Practice Mobile Hacking On
Diving back in or learning a new skill usually requires you to have some type of playground to bang your head against. Here are three that I've been using, and they're somewhat up to date:
In addition to these “mainstream” mobile app targets above there are also many CTF challenges that come out every year that are mobile based. Maintained until 2022, many of these were curated into one spot called the AWESOME mobile CTF repo:
Lastly you have some newer ones that I am keeting my eye on!
This weeks Executive Offensive Newsletter is brought to you by:
Hands-on Full-stack Security Training for Security Engineers
Learn Cloud Security, Kubernetes, DevSecOps, and more. 100% hands-on.
We guide security engineers, architects, and developers to get new skills in AppSec with over 1000+ interactive and hands-on labs. Get 10% off with code “HADDIX10“
/ Platforms and Testing Tools
Next, I wanted to talk a bit about some platforms that make mobile app testing a bit easier for everyone.
First is MobSF, which is a harness for many different tools that perform mobile application assessment tasks. It strings them together via a nice web GUI on Android and offers some static and dynamic analysis of code when it can access it. It also has functions for iOS as well. Many people doing this work full-time use MobSF in some capacity.
The second is Corellium. Corellium is a company that's managed to virtualize the iOS operating system in a way we haven't seen before. Apple has always been very controlling over their ecosystem and operating system. Corellium won a landmark lawsuit against Apple, retaining the ability to offer an iOS virtualized platform. This means they control every aspect of this virtualization, and as an application pen tester, you can pay Corellium for access to their service, install applications on the virtual device, and have direct access to low-level control of the operating system so you can install your tools and perform your tests. I haven't dived deeply into the pricing for Corellium yet, but for people who do mobile application assessment full-time, I'm guessing a high cost is probably not too off-putting.
/ Auxillary
Lastly, I wanted to drop some other free resources that I really like for mobile application security in general.
First of which is NowSecure Academy. After our mobile application assessment team at HP split up, one of my favorite people, Dawn Isabel, went to lead and help develop NowSecure's assessment and binary analysis engines. If Dawn is still there to this day, it says a lot about NowSecure. NowSecure has a free Academy with 14 free modules on mobile application security and mobile security in general.
Second is Sam Bowne’s free hacking classes out fo San Fransico City College. Sam is known for being one of the instructors on the cutting edge in practical cybersecuirty. His classes are often some of the first that make it into the college system for hacking topics. Its amazing. He does one on mobile security! A tremendous resource.
Caludia Ully’s; “The Hitchhacker's Guide to the Mobile Galaxy” is a fantastic workshop that came out of BsidesMunich for FREE. No video but the slides are really full of great info:
Learning through CTF Walkthroughs
One of the things I really like to do is watch the thought process of other hackers. A great way to do this is by reading CTF write-ups. Here are a few that I've gathered. They definitely show how the mindset of a mobile hacker works and the tools and processes they use against different challenges.
/ Wrap Up
Well, to be honest, everyone, there's actually even more I could share on this topic: resources, videos, tips and tricks, etc. But at some point, you have to wrap it up, right?
For now, I'm done working on the mobile project I was on, so maybe on the next mobile project, we'll do a Part 3?
Thanks for sticking with this extra technical and resource-dense two-part series on mobile hacking. Doing these two issues has been super fun and has maybe even inspired me to do a mobile training with Joel himself!
Happy hacking, all!